No business wants to suffer a data breach, but unfortunately, it’s difficult to avoid them in today’s environment. Approximately 83% of organisations have experienced more than one data breach. (IBM Security 2022 Cost of a Data Breach Report). IT Support in London can help.
These breaches hurt businesses in many ways. First, there is the immediate cost of remediating the breach, and then there are the lost productivity costs. You can add the lost business on top of that and lost customer trust. A business could also have extensive legal fees associated with a breach.
According to IBM Security’s report, the cost of a data breach climbed again in 2022. The global cost of one breach is now $4.35 million, up 2.6% from last year. If your business is in the U.S., the cost rises to $9.44 million. In Canada, the average data breach costs companies $5.64 million.
Costs for smaller companies tend to be a little lower. But breaches are often more devastating to SMBs. They don’t have the same resources as larger companies to offset all those costs.
An estimated 60% of small companies go out of business within six months of a cybersecurity breach.
Companies don’t need to resign themselves to the impending doom of a data breach. There are some proven tactics they can take to mitigate the costs. These cybersecurity practices can limit the damage of a cyberattack. All these findings come from the IBM Security report. They include hard facts on the benefits of bolstering your cybersecurity strategy.
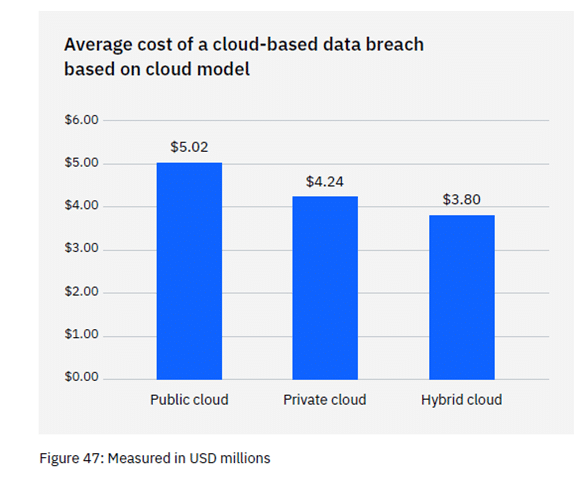
Most organisations use the cloud for data storage and business processes. Researchers found that 45% of all data breaches happen in the cloud. But all cloud strategies are not created equally.
Breaches in the public cloud cost significantly more than those in a hybrid cloud. What is a hybrid cloud? It means that some data and processes are in a public cloud, and some are in a private cloud environment.
What some may find surprising is that using a hybrid cloud approach was also better than a private cloud.
You don’t need to be a large enterprise to create an incident response (IR) plan. The IR plan is simply a set of instructions. It’s for employees to follow should any number of cybersecurity incidents occur.
Here is an example. In the case of ransomware, the first step should be disconnecting the infected device. IR plans to improve the speed and effectiveness of a response in the face of a security crisis.
Having a practised incident response plan reduces the cost of a data breach. It lowers it by an average of $2.66 million per incident.
Zero trust is a collection of security protocols that fortify a network. An example of a few of these are:
Approximately 79% of critical infrastructure organisations haven’t adopted zero trust. Doing so can significantly reduce data breach costs. Organisations that don’t deploy zero-trust tactics pay about $1 million more per data breach.
Using the proper security tools can significantly reduce the cost incurred during a data breach. Using security AI and automation tools brought the most significant cost savings.
Data breach expenses lowered by 65.2% thanks to security AI and automation solutions. These types of solutions include tools like advanced threat protection (ATP). They can also have applications that hunt out threats and automate the response.
Many of these ways to lower data breach costs are best practices. You can get started by taking them one at a time and rolling out upgrades to your cybersecurity strategy.
Working with a trusted IT provider, put together a roadmap. Address the “low-hanging fruit” first, then move on to longer-term projects.
For example, “low-hanging fruit” would be putting multi-factor authentication in place. It’s low-cost and easy to put in place. It also significantly reduces the risk of a cloud breach.
A longer-term project might be creating an incident response plan. Then, you would set up a schedule to have your team drill on the plan regularly. During those drills, you could work out any kinks.
Working with a trusted IT partner takes much of the security burden off your shoulders. Give us a call today to schedule a chat about a cybersecurity roadmap.
Employee Cyber Security Training
Small business are attacked by Hackers 3 x more than larger ones
How to use Chat GPT effectively
You need the best IT support in London. Technology is complicated and expensive. It’s so hard to maintain everything and know what to do when something breaks or goes wrong. IT problems can put a damper on your day. They’re frustrating, time-consuming, and seem like a never-ending cycle of issues.
Penntech’s average NPS score over 90 days is 84. The average Net Promoter Score (NPS) for IT Managed Service Providers (MSPs) can vary. Still, an NPS of around 50 is considered excellent in this industry, with scores above 70 exceptional and rare.
We offer our services on a trial basis for the first three months because we’re confident in our delivery and approach.
Penntech offers a wide range of IT services, from strategic project management to 24/7 remote support, ensuring all your IT needs are always covered.
We provide advanced cybersecurity measures and expertise, including penetration testing services and Cyber Essentials, to protect clients from cyber threats.
We offer Clients the ability to scale IT services up or down based on their needs. This flexibility is crucial for businesses that experience seasonal changes or rapid growth.
Other providers often enforce their preferred IT stack, but we don’t, as IT is not a one-size-fits-all solution.
We ensure our Clients’ business continuity through robust disaster recovery and backup solutions.
With experience in various verticals and industries, Penntech understands different businesses’ unique IT challenges and can provide customised solutions..
Contact us today or explore the range of support packages on offer.


Business owners often have to wear many hats, from handling HR and marketing tasks to managing the finances. One task…

Cool Windows 11 Features That May Make You Love This OS
Microsoft released the Windows 11 operating system (OS) over a year ago. It was well-received mainly with reviews as stable…

6 Ways to Prevent Misconfiguration (the Main Cause of Cloud Breaches)
Misconfiguration of cloud solutions is often overlooked when companies plan cybersecurity strategies. Cloud apps are typically quick and easy to…

The benefits of AI include advancing our technology, improving business operations, and much more. Adoption of AI has more than doubled…

Leading Password Managers for Personal and Business
We hope that your business is already considering a password manager system, but there’s still the matter of finding the…

What’s Changing in the Cybersecurity Insurance Market?
Cybersecurity insurance is still a pretty new concept for many SMBs. It was initially introduced in the 1990s to provide coverage for large enterprises. It covered things like data processing errors and online media.

What are the advantages of implementing Conditional Access?
It seems that nearly as long as passwords have been around, they’ve been a major source of security concern. Eighty-one…

The SME Guide to Microsoft 365 Copilot
Artificial intelligence is reshaping the way businesses work—and nowhere is this more evident than in Microsoft 365. With Copilot now…

AI Attacks and the Role of Backups
Artificial intelligence (AI) is transforming cybersecurity – both for defenders and attackers. While businesses adopt AI-powered tools to strengthen protection,…

AI in Cyber Security: Friend or Foe?
Artificial Intelligence (AI) is rapidly changing the way businesses operate — including how they protect themselves from cyber threats. For…

Avoiding Costly Downtime in 2025
In today’s digital-first world, businesses rely more than ever on constant connectivity and system availability. Yet despite modern advances in…
MSP Insights: ISO 27001 in Practice
In 2025, data protection and cyber resilience remain top priorities for businesses of all sizes. ISO 27001, the international standard…

SharePoint: The Future of File Storage
For many years, traditional file servers were the backbone of business operations. They provided shared drives where employees stored documents…

As cybersecurity risks evolve, so too must the standards and frameworks designed to protect organisations. In April 2025, the National…

Managing Multi-Tenant Environments – Best Practices for 2025
As businesses adopt more cloud services and expand globally, managing multi-tenant environments has become a critical challenge for IT teams…

Why Cyber Insurance Isn’t Enough
Cyber insurance has become a popular safety net for organisations worried about the growing threat of cyber attacks. While having…